Evgen verzun
Blog
September 5, 2019
Over 419 Million Phone Numbers Exposed. How To Learn From Facebook’s Mistakes To Never Repeat Them Again
When you get the headlines that involve hundreds as numbers, “data” as a noun, and “exposed” as an adjective, you already know who’s involved.
Is it even necessary to point fingers at Facebook at this point?
They don’t feel any shame for all the leaks that happened in the past few years. As we can see, expecting them to learn from their mistakes is not an option anymore.
There will be more fines, more high-resolution photos of Zuckerberg plastered all over the media, and even more angry users.
Not A Pretty Sight, No Matter How You Look At It
But we can look at this situation with an exposed server differently, abstaining from pointless verbal obliteration and sticking to ways of ensuring our companies never get in the same situation.
Let’s look at how Facebook’s spokesperson reacted to such news...
“The dataset is old and appears to have information obtained before we made changes last year.”
Facebook, if you don’t need that information, it doesn’t mean that anyone else is the same.
It still can give malicious actors the power to reset accounts. They can also pull up more information about the person through public databases, expose the target to annoying spam or even subject the target to an impersonation, gaining access to bank accounts
But wait, there’s more!
The most recent data uploaded to that server dates back to July of 2019. So someone is either lying or has no idea what’s happening.
Plus the exposed information included users' Facebook IDs. But that’s not the end of the world for one simple reason - everyone could see it anyway in the URL.
Every Lesson Is A Blessing?
Let’s recap now.
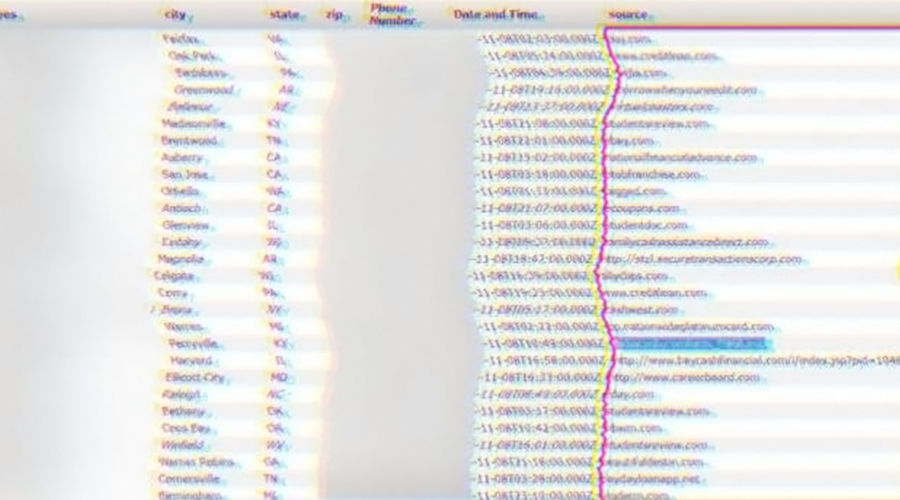
Personal information has been gathered by a third party, the database did not have any password protection, and no signs of encryption were seen, as phone numbers were available in plain text to anyone who could find them.
I assertively repeat the number one rule in cybersecurity today - data should always be encrypted, in transit and at rest.
That’s an important rule, but not the only one.
- Encryption should transpire on the client’s side.
- Only a client should have access to encryption keys.
- We should not transfer sensitive data and files via unprotected communication channels.
- The company must be in full control of the storage with encrypted information and keys.
- Cybersecurity solutions must be legally compliant.
So how many cases should we go through, and how many billions they should pay in fines to understand this? I would like to see Facebook change, but tigers don't change their stripes.