Evgen
Verzun
Blog
Founder, Inventor, Crypto- and Cyber- security expert, System and Software Architect
I’m always open to new contacts, ideas and initiatives.
If you have interesting information, idea, proposition, or I can help you, don’t hesitate to contact me.
April 22, 2026
The Mythos Paradox and a Critical Backdoor in Anthropic’s MCP
Anthropic’s Mythos can find serious bugs, but its own MCP system has a built-in command injection flaw. Because it executes unsanitized commands, attackers can run arbitrary code. Anthropic calls it “by design,” creating a major security contradiction.
February 18, 2026
The Phishing Playbook for 2026: AI Translation and the End of “Bad Grammar”
AI has made phishing more dangerous, with polished, convincing attacks at scale. As old warning signs fade, users must verify context, use MFA, and treat unexpected requests cautiously.
January 29, 2026
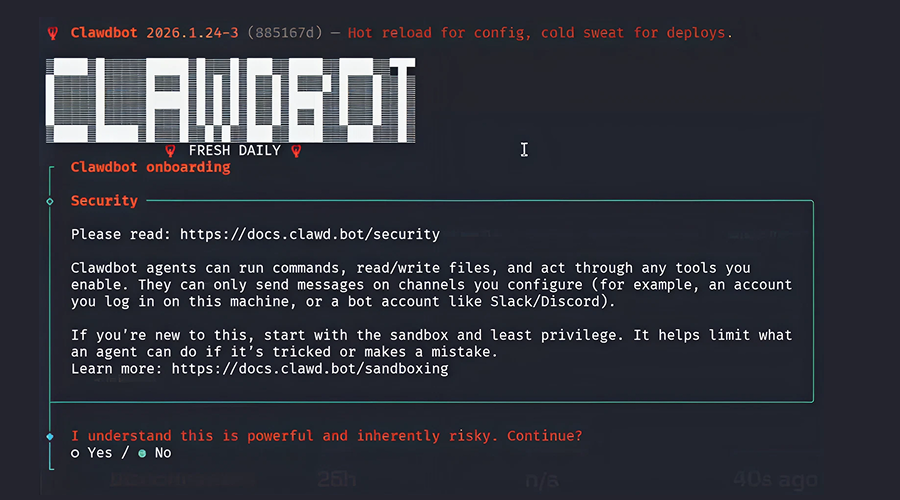
Moltbot: A Brilliant Idea with a Built-In Security Time Bomb
January 29, 2026
Moltbot: A Brilliant Idea with a Built-In Security Time Bomb
Moltbot is powerful, open-source, and dangerously trusting. A single prompt injection is all it takes to turn automation into compromise.
November 14, 2025
The AI Security Wake-Up Call: Lessons from Real Breaches
November 14, 2025
The AI Security Wake-Up Call: Lessons from Real Breaches
I’ve been building software long enough to remember when “cloud” meant someone else’s server and a leaked spreadsheet was just a bad day, not a crisis requiring forensic analysts. Fast forward to today: AI promises speed, insight, and automation. Yet, every time I read another story about data leaks, exposure, or governance failures, I’m reminded […]
November 13, 2025
The Era of Digital Identity, Defined by HyperID
November 13, 2025
The Era of Digital Identity, Defined by HyperID
Digital IDs are becoming more common in official places. However, because adoption is uneven and the technology isn’t perfect, the headlines are basically: “Welcome to the future ─ also, carry paper.” HyperID is changing how we think about digital identity by moving us from carrying stacks of physical documents to the ease of a single […]
Load more
⨯
My blog couldn't proceed your request right now.
Please try again a bit later.
⨯
Thank you for contacting me!
I will get back to you as soon as I can.
⨯
Contact me
⨯
My blog couldn't proceed your request right now.
Please try again a bit later.
⨯
Thank you for subscribing!
I added you to my emailing list. Will let you know as soon as I have something interesting.
⨯
Subscribe for email updates
Want Blog Updates?